How to store aes encryption key images are available. How to store aes encryption key are a topic that is being searched for and liked by netizens today. You can Get the How to store aes encryption key files here. Find and Download all royalty-free vectors.
If you’re looking for how to store aes encryption key pictures information connected with to the how to store aes encryption key topic, you have pay a visit to the right blog. Our site frequently provides you with hints for downloading the highest quality video and picture content, please kindly surf and find more informative video articles and graphics that fit your interests.
How To Store Aes Encryption Key. To communicate a symmetric key and IV to a remote party you would usually encrypt the symmetric key and IV using asymmetric encryption. Best way to store encryption keys inNET C 5 Generally a new key and IV should be created for every session and neither the key nor IV should be stored for use in a later session. 28072018 Preparing your environment to use AES encrypted passwords. 16042013 Your data that needs encrypting can then be encrypted with the AES key and the AES key encrypted with the pub key from your stored key pair.

 Encryption And Hashing For Laravel Developers Part 1 Symmetric Encryption Josip Crnkovic From crnkovic.me
Encryption And Hashing For Laravel Developers Part 1 Symmetric Encryption Josip Crnkovic From crnkovic.me
String aesEncrypted aesEncryptencrypt StringContent. Theres really no safe way to store keys and have them accessible to a web app. 05082018 The key rotation period should depend on your needs. Best way to store encryption keys inNET C 5 Generally a new key and IV should be created for every session and neither the key nor IV should be stored for use in a later session. Well these are my opinions. Obviously Im not going to use that one since the key will be stored in plaintext.
Before executing these steps you will need to have.
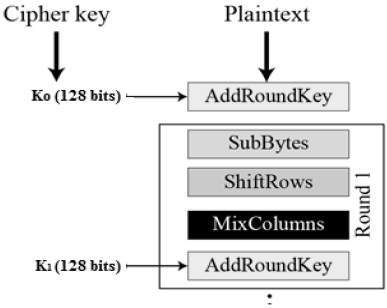
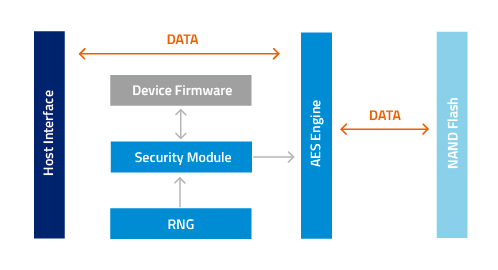
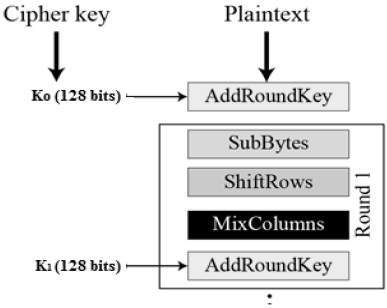
20082013 Store the key on disk and at the OS level configure file access so that only the account your application is running under can read the file the key is contained in. Use the Powershell below to get your environment prepared. 20082013 Store the key on disk and at the OS level configure file access so that only the account your application is running under can read the file the key is contained in. 1 a secure location to store your key 2 a secure location to store your encrypted password 3 the password for the User account that you need to use in your script. 09052011 AES symmetric algorithm where encryption and decryption key is the same is used for instance within Group Policy passwords set by group policy preferences to encrypt those passwords in the xml file being part of the group policy definition stored in SYSVOL. As mentioned earlier once we have our data arrangement there are certain linked operations that will perform the scramble on each state.

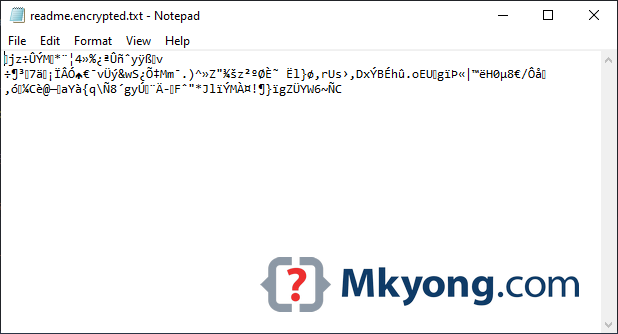 Source: mkyong.com
Source: mkyong.com
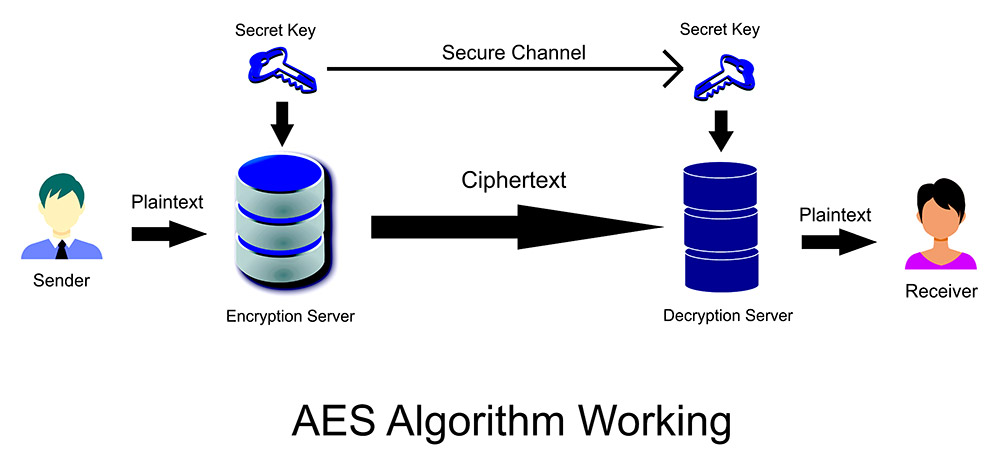
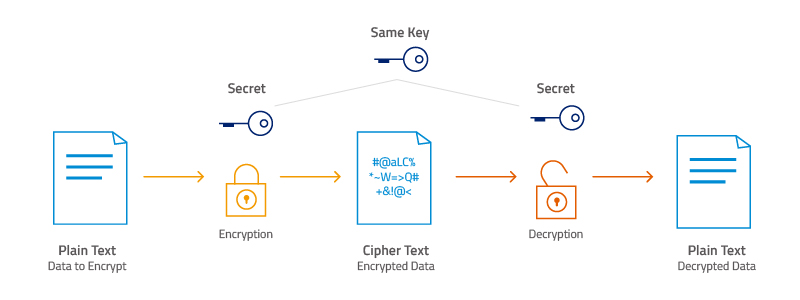
The purpose here is to convert the plaintext data into ciphertext through the use of a secret key. If you use a password hash as an encryption key you should not store the hash for login purposes. That being said the safest. What this means in practice is that a password or passphrase becomes part of the key and so data encrypted with AES can only be decrypted with the correct password or passphrase. Not secure in the least.
 Source: help.bizagi.com
Source: help.bizagi.com
User has a password that is used to encrypt the encryption key - Pretty secure and usable. When you need to decrypt you decrypt your AES key then decrypt your data. When dealing with just ONE private key as in the question the best way is to store it on a smartcard. Most smartcards can store a small amount of private keys. That being said the safest.
 Source: atpinc.com
Source: atpinc.com
Well get into the order of the operations in the next section. Very secure very usable. At the end of the day its about key. What this means in practice is that a password or passphrase becomes part of the key and so data encrypted with AES can only be decrypted with the correct password or passphrase. In order to decrypt I have to upload a temporary file with my private key and retrieve the necessary data.
 Source: researchgate.net
Source: researchgate.net
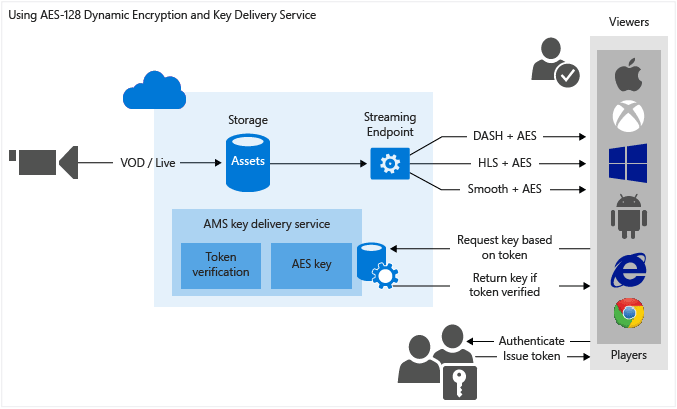
To communicate a symmetric key and IV to a remote party you would usually encrypt the symmetric key and IV using asymmetric encryption. Alternatively if you have a small amount of data you could skip the AES encryption entirely and use RSA encryption. Well get into the order of the operations in the next section. String aesEncrypted aesEncryptencrypt StringContent. To communicate a symmetric key and IV to a remote party you would usually encrypt the symmetric key and IV using asymmetric encryption.
 Source: pro-bravia.sony.net
Source: pro-bravia.sony.net
04022019 Because its a symmetric encryption algorithm in AES there is is just the one key which is a shared secret between the sender and recipient so no privatepublic key pairs. Or even much better let the crypto hardware on the card generate the required private keys for you. Well these are my opinions. The card let you use them but they can never be extracted from the card. The file could be a flat file or an encrypted container thats protected by a password which your application knows up to you to decide but an encrypted container is better.
 Source: section.io
Source: section.io
Theres really no safe way to store keys and have them accessible to a web app. Most smartcards can store a small amount of private keys. Alternatively if you have a small amount of data you could skip the AES encryption entirely and use RSA encryption. 23042020 What the 4 AES Encryption Operations Are and How They Work. 09052011 AES symmetric algorithm where encryption and decryption key is the same is used for instance within Group Policy passwords set by group policy preferences to encrypt those passwords in the xml file being part of the group policy definition stored in SYSVOL.
 Source: docs.microsoft.com
Source: docs.microsoft.com
Or even much better let the crypto hardware on the card generate the required private keys for you. Very secure very usable. 23042020 What the 4 AES Encryption Operations Are and How They Work. Well get into the order of the operations in the next section. 29072019 AES Encryption Keys password hashing Gerrit Jansen van Vuuren.
 Source: trentonsystems.com
Source: trentonsystems.com
Well get into the order of the operations in the next section. Learn how to create a secret key for encryption and decryption using Android KeyStoreSubscribe to my weekly newsletter. 16042013 Your data that needs encrypting can then be encrypted with the AES key and the AES key encrypted with the pub key from your stored key pair. Very secure very usable. Obviously Im not going to use that one since the key will be stored in plaintext.
 Source: trentonsystems.com
Source: trentonsystems.com
9 horas atrs Im trying to encrypt a file using aes encryption and split the key with shamirs secret sharing. The four types of AES operations as follows note. 28072018 Preparing your environment to use AES encrypted passwords. 23042020 What the 4 AES Encryption Operations Are and How They Work. As mentioned earlier once we have our data arrangement there are certain linked operations that will perform the scramble on each state.
 Source: crnkovic.me
Source: crnkovic.me
When you need to decrypt you decrypt your AES key then decrypt your data. 20082013 Store the key on disk and at the OS level configure file access so that only the account your application is running under can read the file the key is contained in. To communicate a symmetric key and IV to a remote party you would usually encrypt the symmetric key and IV using asymmetric encryption. 05082018 The key rotation period should depend on your needs. In order to decrypt I have to upload a temporary file with my private key and retrieve the necessary data.
 Source: atpinc.com
Source: atpinc.com
Alternatively if you have a small amount of data you could skip the AES encryption entirely and use RSA encryption. Use the Powershell below to get your environment prepared. StringEncrypter aesEncrypt new StringEncrypter aesKey aesKeygetAlgorithm. The file could be a flat file or an encrypted container thats protected by a password which your application knows up to you to decide but an encrypted container is better. The card let you use them but they can never be extracted from the card.

This site is an open community for users to submit their favorite wallpapers on the internet, all images or pictures in this website are for personal wallpaper use only, it is stricly prohibited to use this wallpaper for commercial purposes, if you are the author and find this image is shared without your permission, please kindly raise a DMCA report to Us.
If you find this site convienient, please support us by sharing this posts to your preference social media accounts like Facebook, Instagram and so on or you can also bookmark this blog page with the title how to store aes encryption key by using Ctrl + D for devices a laptop with a Windows operating system or Command + D for laptops with an Apple operating system. If you use a smartphone, you can also use the drawer menu of the browser you are using. Whether it’s a Windows, Mac, iOS or Android operating system, you will still be able to bookmark this website.





